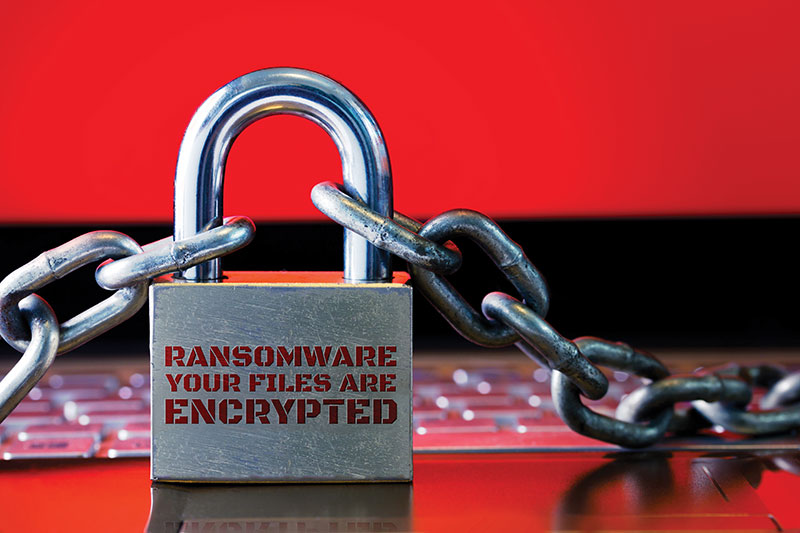
A prominent threat since the mid-2000s, ransomware attacks continue to plague businesses large and small – and they’ve grown more sophisticated over time.

Ransomware is a kind of computer malware that encrypts and blocks access to computer files until a ransom is paid. It targets both human and technical weaknesses and is delivered in multiple ways.
In 2019, the FBI’s Internet Crime Complaint Center (IC3) received 2,047 ransomware complaints from American companies, a 37% increase over 2018. The actual number was probably much higher, because only a small percentage of attacks are reported. Across the globe, there were an estimated 204 million ransomware attacks in 2018.
Ransomware is the fastest growing type of cybercrime, according to Cybercrime Ventures. Every 14 seconds across the globe, a business falls victim to a ransomware attack.
As ransomware attacks have evolved, the business risks have drastically increased.
Risk No. 1—Financial
Most early ransomware attacks affected a single system, and payments to decrypt the files were typically under $500. Today, entire networks are encrypted in a single attack, and the ransom demanded can easily go into millions of dollars.
In 2019, the 2,047 ransomware attacks reported to the FBI had adjusted losses of nearly $9 million. Globally, ransomware attack losses were $11.5 billion in 2019, according to Cybercrime Ventures. The company predicts that global ransomware damage will hit $20 billion in 2021.
Ransomware attackers have created a tiered pricing structure to leverage more payment depending on the importance of services provided. A workstation might be priced at $2,000, while an email server might be hundreds of thousands to decrypt.
In recent years, some organizations have had to shut down because of the overwhelming financial burden of these types of attacks. Even without the ransom payment, the cost of restoring IT operations can be steep.
Risk No. 2 – Disruption to Operations
As cybercriminals have moved towards mass encryption of all systems in a network instead of a single system, the risk of major disruptions to business operations increases exponentially.
The question organizations need to be prepared to answer is this: “If we woke up tomorrow and all of our computers were unavailable, how could we continue to conduct business?” Even with backups, entire network-wide interruptions take days or even weeks to recover, which can cause major disruptions.
Risk No. 3—Reputation
When organizations choose not to pay a ransom to recover their IT systems, cybercriminals can include extortion demands to ensure payment is received. These criminals attempt to steal sensitive information in the days prior to organizations learning that their computers have been compromised.
Risk No. 4 – Compliance issues
When businesses and organizations maintain regulated data, such as personally identifiable data, financial information or electronic patient health records, data breaches from ransomware attacks can cause compliance issues. Organizations need to consider the access level gained during the attack and whether their systems hosting regulated data were accessed. Organizations must conduct good-faith risk assessments to determine how likely it is that protected health information was accessed or extracted.
How to protect your organization
Most ransomware attacks happen in phases. The initial phase is to compromise one computer; next, the hackers gain elevated access on the network. The third phase is to spread, and then to identify and steal sensitive data. The final phase is executing the ransomware.
Each phase will leave artifacts that cybersecurity professionals and proper technology can identify and block. If organizations practice basic cybersecurity hygiene, most attacks can be stopped early in their tracks.
Basic cybersecurity hygiene includes:
Prevention
• Make sure antivirus software is deployed to all systems, is consistently updated and configured to block and alert administrators to malware.
• Regular security assessments can help organizations identify and correct weaknesses.
Detection
• All security alerts should be investigated and cleared.
• Ensure that firewall, endpoint and web filter logs are retained for at least 30 days.
Response
• Implement the 3-2-1 backup strategy: Have at least three copies of your data in two different media formats, with one of the copies held offsite. If cybercriminals compromise your backups during the attack, you will be unable to recover. ■
Gui Cozzi is cybersecurity practice leader at Dean Dorton, a Kentucky CPA accounting firm with an IT security/tech consulting division.













Add Comment