
The meeting starts in 10 minutes, your report is first on the agenda, and the printer is acting up again. You pace in front of the printer, willing it to just work this time, but the error light starts flashing. You shake your head and go back to your desk to find another solution.
After the meeting, you fire up your browser to search for new printers. You’re surprised at how many affordable, high-performance options you find, so you toss a few into your shopping cart and plan to narrow down the choice later.
Your search is interrupted by a phone call; you close your browser and forget about it – until later, when upon logging onto Facebook the first ad you see is for the exact printer you were considering online this morning. It’s amazing – and yet, scary.
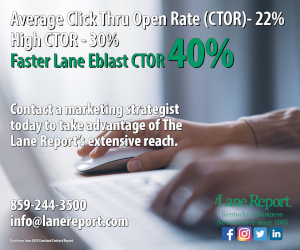
- IT’S FREE | Sign up for The Lane Report email business newsletter. Receive breaking Kentucky business news and updates daily. Click here to sign up
This scenario takes place many times every day. We discuss how strange it is with friends and coworkers, but rarely take time to figure out how it occurs or whether we’re truly OK with it. We accept it as a price we pay for the convenience of having internet access and quickly turn our attention elsewhere.
The process that serves up these individually aimed advertisements is called targeted ad tracking or online behavioral tracking. It is made possible by web “cookies”: coding built into webpages that interacts with browsers to collect information about visitors. When you visit a webpage (especially for a product), a cookie is created on your computer. When you click to go to another page, its server first scans your browser’s cookies and loads ads related to your recent online activities.
Cookies are a convenient way to accumulate and carry information from one session on a site to the next visit, or between sessions on related websites, according to the website whatarecookies.com. For example, cookies can store your username and password for a site so that you don’t have to log in every time you visit.
A specific type called a tracking cookie, however, can share info among many websites or services. Tracking cookies gather a history of the user’s actions on multiple sites and transmit it to the originator – and often its customers.
“Cookies are used extensively,” said Joe Danaher, chief information security officer of Integrity IT, a Lexington-based information technology services firm. “They identify your IP address. They identify and send (a history of) the websites you’ve visited, the searches you’ve conducted, even the purchases you make online. They can collect all this information silently. It’s just a byproduct of going to these websites.”
Currently, targeted ad tracking is a threat to personal privacy, but it is not a business-level threat, Danaher said.
Yi Hu, a professor in the Department of Computer Science at Northern Kentucky University, agreed. His research concentrates on data security, data mining, information assurance, database systems and trust management in cyberspace.
“It is more of a personal privacy issue as it is more related to internet browsing, purchase, and social behavior of an individual,” Hu said. “As most targeted ad tracking is disseminated via web browsers and targeted at a specific group of users, it is more of a concern for individual internet users.”
Oversharing is a threat to business
A larger threat to a company’s privacy is the oversharing of information on social media by employees, Danaher said.
“People pretty much share all aspects of their lives on social media,” he said. “Your work life is part of that.”
Oversharing is risky because cybercriminals use social media platforms to conduct open-source intelligence gathering, Danaher said, which does not violate any laws. Potential criminals can learn where people work, what their interests are, the format of their company email addresses and more by examining social media posts.
“For example, on Instagram, there’s a hashtag called #newbadge,” he said. “People who are proud they have new jobs take pictures of their employee badges (and post them) with the hashtag #newbadge. A lot of times it has their name on there, what department they work for and what company they work for. Also, they’re giving away the format of that badge. So, if I’m a criminal, I can print up a badge, go on site, put a USB drive in an open computer and I’ve got access to your network.”
Because personal interests are readily posted on social media, cybercriminals can use that information to send a believable spear phishing email to them that contains malware. They only need the target recipient to click one link, Danaher said.
Phishing is the practice of sending fraudulent emails or instant messages that purport to be from reputable companies to get recipients to reveal personal information. And spear phishing emails target specific individuals or companies, with attackers typically using personal information about the target to increase their likelihood of success.
(See the Glossary of Terms on page 39 to learn more cybersecurity key words and phrases.)
“People share their data on social media and just readily give it away. That oversharing is what we’re seeing as a bigger threat to businesses, more so than online behavioral tracking,” Danaher said. “People don’t even realize that something they’re posting could be used against the places they work.”
To mitigate this risk, businesses should talk to employees about what’s appropriate to post, and create and enforce social media policies for their business, he said.
You are the product on free sites
Online platforms of webpages or associated sites collect information about people and their interests and then sell that information – or access to it – to advertisers, said Gui Cozzi, cybersecurity practice lead at Dean Dorton, an accounting firm and business consultant with offices in Louisville and Lexington, Ky., as well as Raleigh, N.C. Such info allows advertisers to accurately find potential customers and target them directly, he said.
Cookies can be placed and collected by organizations that profile and track customers across websites and devices, especially if users are taking advantage of free online services.
“A good rule of thumb is: If you are enjoying an online service for free, most likely their business model is selling information that they are collecting about you,” Cozzi said. “Facebook is a great example of that practice and some of the Google services as well.”
Firms that collect this personal information and sell it to other businesses, he said, also sometimes aggregate browsing information with multiple other data sources, including loans that are made public, credit card information or shopper’s card points, for example, he said.
Louisville marketing agency El Toro is an IP targeting company whose noncookie process precisely matches physical addresses and computer IP addresses. Its products can let an advertiser aim to give a user repeated exposure to a product a specific number of times or over a specific timeframe – if the rate that advertiser has “bid” is higher than those of others who want their message presented to users with profiles they value.
The split-second lag between clicking onto a page and when its advertising messages load can involve the platform querying a variety of ad server networks to see who has bid the highest rate to reach users having the aggregated data profile matching what’s attached to the incoming IP address.
Any business that sells products or services online can use and benefit from targeted ad tracking. In fact, most online shopping sites collect information about their users, Danaher said.
“That covers ordering a pizza from Domino’s, buying some shoes from Nike and everything in between that has a place online where you can make a purchase,” he said.
That information is very valuable to online sellers. Marketing campaigns have always concentrated on trying to influence consumers, said Scott Logan, technical director of security at NetGain Technologies, headquartered in Lexington. Tracking consumers’ online activity allows businesses to advertise to consumers they already know are interested in their product, making them a qualified prospect.
A user’s browser history or recent purchase history can be used to put a product of current interest in front of them, Logan said.
Even though there are concerns about privacy, some people think it is better to see advertisements that interest them rather than ads from “spray and pray” marketing, where a business advertises its products or services everywhere to everyone and hopes it reaches those interested in its product.
Google and Yahoo offer ways to adjust your personal ad preferences and learn how and why advertisers are targeting you, Danaher said. You can also see the content that has been gleaned from your browsing and search history. (Take a peek at your information: visit adssettings.google.com or myactivity.google.com while logged in to your Google account.)
It is important to remember that online content is not truly free. Content on all media platforms – whether physical like this magazine, broadcast, digital or other – is paid for by advertising, which “has been around for a long time,” Danaher said.
“That’s what helps keep online services free or very low cost. It is the way these websites generate revenue,” he said. “That’s how Google started, and I don’t know if any of us can imagine not having Google or it not being free.”
Is tracking a privacy threat?
Though very common and widely accepted, targeted ad tracking is a threat to personal privacy.
“The big privacy concern is that you never voluntarily said you would provide this information,” Danaher said. “You were never asked. You’re not aware, by and large, what is being gathered on you.”
Countless advertising networks secretly monitor users across multiple websites and build detailed profiles of their behavior and interests, according to the Electronic Frontier Foundation (EFF). It seems invasive, Cozzi said, but the actual privacy risks are minimal.
The bigger danger is private user data being used to manipulate or influence large numbers of people, he said. Privacy advocates such as EFF, the Electronic Privacy Information Center (EPIC) and others are working to help consumers regain control over their personal data and limit abuse of consumer profiling.
“A lot of people who really advocate for privacy are sounding the alarm that this kind of data collection and aggregation makes it easier for governments to weaponize and use it to polarize our enemies or…influence the outcome of an election,” Danaher explained.
Privacy concerns are on lawmakers’ radar. In the European Union, a new statute called the General Data Protection Regulation (GDPR) went into effect last spring. It requires any business that collects personal data to notify users what information is being gathered, how it will be used and who will be using it. Consumers must grant consent before their data is collected, and anyone can opt out. The regulation applies to any company that markets goods or services to EU residents, regardless of its location.
Citizens’ rights to protect their personal data must be safeguarded, the European Commission said.
That sentiment has not caught on in the United States, Danaher said.
“There’s a different view of this (collected) information as far as whether it really is your information, to be quite honest,” he said.
The U.S. does not have a single, comprehensive federal law regulating the collection and use of personal information. Instead, a combination of federal and state laws applies. There has been increasing discussion on the topic, however; last year, several congressional hearings focused on the data practices of Facebook, Twitter and Google.
Online behavioral tracking is still in its infancy, and the privacy risks will only increase as the practice evolves, Danaher said.
“It’s not at the ‘Minority Report’ level yet, but as machine learning, artificial intelligence and processing power to run those algorithms progresses, I think you are going to see this data can get stolen and maybe used for more criminal activity,” he said.
There is always a chance that data collected about users and stored on servers could be compromised. Some big-name companies have experienced massive data breaches in recent years, including Equifax in 2017 (143 million affected); Yahoo in 2013-2014 (3 billion affected); Marriott in 2018 (500 million affected); and Anthem in 2015 (78.8 million affected), among others.
Phishing, malware still risks to business
Although phishing has been around for years, it remains one of the greatest business cybersecurity threats. Phishing emails are meant to get money quickly with minimal effort, so they are sent to a large number of email addresses. Cybercriminals only need a few recipients to fall for them.
“We are seeing a lot of small business getting into phishing situations where they are being tricked into sending payments or paying an invoice that is fraudulent,” Cozzi said. “Especially in small companies without a formal billing system.”
Spear phishing emails are more targeted and the goal is to compromise the target user’s computer or get a foothold into their network, Danaher explained. If the cybercriminal can get the user to click a link or attachment, they can access the network. They often search online for the perfect target and customize the email to be more effective.
“That’s what we’re still seeing as the No. 1 threat at a business level,” he said.
Some of these phishing attempts will look authentic at first glance, but can be recognized as fraudulent upon inspection. For example, a cybercriminal may try to mimic a popular company name like Amazon by replacing the ‘m’ with the letters ‘r’ and ‘n’, making the email address end in arnazon.com, which slightly resembles the correct address.
“One of the biggest things we’re seeing is people being tricked into giving away their email credentials,” Danaher said. Cybercriminals will send an email that looks legitimate, and get the recipient to “login” to one of their accounts. Once the user puts in their username and password, the hacker has that information.
“A lot of times, they’ll just sit there and learn everything they can about your network, especially your financial transactions, who you usually pay,” Danaher said. “That’s why finance and C-level folks are usually a big target for this type of scam.”
Ransomware and malware are also common problems faced by businesses. The threat level is much larger with ransomware, Cozzi said. It involves hackers installing malicious software designed to block access to a company’s computer system until a sum of money is paid.
“It is an easy way for hackers to get a little bit of money and it works. And they do it many times a day,” he said.
Another threat is CEO fraud or business email compromise, which is associated to wire fraud. Emails are forged to elicit funds to be sent on request of a spoofed CEO email account, Logan said.
“The list of cyberthreats or attacks that threaten businesses is a long one,” he said. Some of those include formjacking, botnet attacks, cloud attacks and supply chain attacks.
Awareness, education are the best defense
Businesses of all sizes are at risk. Experts advise that cybercriminals do not discriminate; they just want the money.
Companies can mitigate their cyberthreats by first learning where they are vulnerable. A risk assessment by an IT services provider will offer specific information about a business’ risks and where improvements can be made. That information can assist management in formulating the company’s cybersecurity policies.
Cybersecurity needs to be a priority from the top down, Cozzi said. A company’s leadership team needs to understand the risks.
“There’s a financial risk and a reputation risk,” he said. “You could potentially lose customers or have to be enrolled in a data breach situation.”
Here are a few cybersecurity tips for businesses:
• Know your risks. If you have highly sensitive information, take extra steps to protect it.
• Use multifactor authentication to access your email.
• Educate all employees about cyberthreats. Train them to spot a phishing attempt. Some companies periodically send a fake phishing attempt to their employees to see if they catch it and report it to their internal IT teams.
• Create and enforce social media policies.
• Require employees to use strong passwords and change them often.
• Install antivirus software and antispyware. Remember, you get what you pay for.
• Secure your network with a firewall and encrypting information.
• Be prepared for an attack. Enlist the help of an IT provider that is prepared to quickly respond to an attack.
• Back up your data and have it available for recovery.
• Control physical access to computers and networks.
• Create a mobile-device action plan. Require mobile-device users to password protect their devices and install security apps to prevent criminals from stealing information while the phone is on public networks.
• Protect all pages of your public websites, not just the signup and checkout pages.
Freaked Out by Ad Tracking? Here’s How to Stop It
If you are troubled by having information collected about you and used all over the internet to target you, there are some things you can do to sidestep tracking ads.
First, periodically clear your cookies on each of your devices. (A quick internet search will tell you how to do that on each of your browsers.) Be prepared to reenter passwords and other information on sites you visit frequently, since cookies store that information.
Some other tips:
• Purge your Google ad history by visiting myactivity.google.com.
• Use the “hide ad” function available on some sites, such as Facebook.
• Install an ad blocker or use a private browser. Consider installing a tracker blocker.
• Reset your advertising ID on your mobile device. (Use the settings function on Apple and Android devices to get to these options.)
• Opt out. Visit the Digital Advertising Alliance’s WebChoices Tool page at optout.aboutads.info to scan your cookies and opt out of advertising for specific companies or all of them.
How Safe Are Listening Devices?
Nearly a quarter of U.S. households own some sort of smart speaker or assistant such as Google Home or Amazon Alexa. The devices are inexpensive and can be fun to use. But they are always listening, and that can be problematic. Especially if the devices are used in a place of business.
“Are we willing to trade a little bit of our privacy to enjoy some free online services? I think that’s what we see with these listening devices,” said Dean Dorton’s cybersecurity practice lead, Gui Cozzi. “Privacy is an interesting concept: On one hand, people are concerned about that; on the other hand, they provide their information willingly to all kinds of devices.”
Amazon recently admitted that it employs thousands of full-time workers to listen to what customers say to Alexa and transcribe the voice commands. The information is fed back into the software to help improve Alexa’s grasp of human speech. Amazon said only a small number of interactions with random customers are annotated, noting that it takes the “security and privacy of our customers’ personal information seriously.”
Information gathered by smart speakers, smart home assistants or mobile devices that use voice commands are stored with the vendor of the device, on its servers or cloud services, said Yi Hu, a professor in the Department of Computer Science at Northern Kentucky University. Anyone concerned about how much their device is listening should check with the device vendor to see how they collect, process and save user data, he said.
Businesses that deal with intellectual properties, national security matters or confidential information should probably not use smart speakers in their offices.
“You want to be cognizant that you don’t talk about sensitive matters when you have these devices installed,” Cozzi said.
Glossary of Terms
Botnet: a number of internet-connected devices, each of which is running one or more bots. They allow the attacker access to the device and its connection, and can be used to perform distributed denial of service attacks, steal data or send spam.
Cookies: small pieces of data sent from a website and stored on a user’s computer by the user’s web browser. Cookies were designed to allow websites to remember information or to record the user’s browsing activity. They can also be used to remember data previously entered in form fields. Tracking cookies are commonly used to compile long-term records of browsing histories.
Formjacking: the use of malicious code to steal credit card details and other information from payment forms on checkout pages of e-commerce sites.
Malvertising: the use of online, malicious advertisements to spread malware and compromise systems. Generally, this occurs through the injection of unwanted or malicious code into ads on legitimate websites.
Malware: software that is specifically designed to disrupt, damage or gain unauthorized access to a computer system.
Phishing: the fraudulent practice of sending emails or instant messages purporting to be from reputable companies in order to induce individuals to reveal personal information, such as passwords and credit card numbers.
Ransomware: a type of malicious software designed to block access to a computer system until a sum of money is paid.
Spear phishing: phishing attempts directed at specific individuals or companies. Attackers gather and use personal information about their target to increase their probability of success.
Supply-chain attacks: attacks that occur through a third-party vendor that has been compromised.
Lorie Hailey is a special publications editor for The Lane Report. She can be reached at lorie@lanereport.













The illegal attempts are basically done by a scammer to steal the users’ personal information for their fraudulent attacks. They can also take guidance instructed by Netgear EX6100 Setup that will help them efficiently.
Lots of good work here. As a Google and Bing Accredited digital marketing practitioner who spends every work day in this space, I hope you don’t mind me playing devil’s advocate from the advertisers and business POV. Programmatic advertising is a godsend for business, simply stated. It has revolutionized marketing and in some ways leveled the playing field.
Imagine being a patio store but not being able to target local homeowners for your Spring promotion with a limited budget? With programmatic, you can even target local homeowners who are in the market for lawn furniture, have recently been looking at landscaping services and have disposable income. You won’t have any idea who they are *exactly* – but you can choose to show ads to the PERSONA meeting these criteria. Everyone wins.
Well, everyone who does it well wins. This morning I saw ads for forklift parts. Not something I use often here at BuzzMaven. I have seen ads for tractor trailer safety equipment and, lord help us, scented candles.
Access to programmatic/targeted advertising marketplaces provides businesses a much better option than random methods that existed before. These would drain ad/marketing budgets with minimal results or ability to optimize – limiting potential and even causing many businesses to close.
The legitimate and smart use of targeted ads can level the playing field in a market increasingly dominated by huge, automated marketplaces.
There is cognitive dissonance in play: Surveys show 70-80% of consumers prefer this kind of relevance in ads they see, but only 17% agree with tracking. I’d guess nearly 100% of business owners favor programmatic availability. I think the reason for the huge disparity is a lack of understanding of technology – including how the targeting is to a persona, not a person, on most major networks.
GDPR/CCPA and other is a healthy consumer-focused framework allowing people to opt-out as they wish are going to permeate the web. We’ll see how many actually do. I’m predicting under 5%.
Scott Clark
BuzzMaven, Inc. – Lexington