 By Lorie Hailey
By Lorie Hailey
Thousands of Kentuckians are now working from home to help prevent the spread of COVID-19, an especially contagious virus that causes respiratory complications and death at much higher death rates than typical seasonal illness.
Nearly two weeks ago, Gov. Andy Beshear encouraged all Kentucky businesses to allow their employees to work from home to promote social distancing. To implement this, business owners had a tall order: Determine how to best serve their clients and customers during this global pandemic; make sure their employees have the correct equipment and infrastructure to do their jobs from home; find ways to virtually communicate with staffs; and keep their businesses running smoothly. And all of this had to be done quickly.
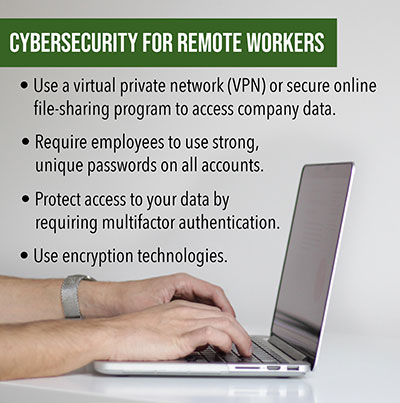
In the whirlwind of adjusting to this new normal, companies should be careful to not overlook cybersecurity, Kentucky IT professionals say. Protecting data and preventing cybercrime should remain a top priority.
“Don’t let security be a casualty of supporting remote workers,” said SimplifIT, a Frankfort-based managed services and cybersecurity firm.
Part 2 of this series discusses cybercrime threats related to coronavirus and offer tips on practicing good cybersecurity hygiene while working from home.
For some businesses, a virtual private network, or VPN, might be the best fit, said Gui Cozzi, cybersecurity practice leader at Kentucky-based Dean Dorton, a CPA accounting firm with an IT security/tech consulting division that has locations in Raleigh, N.C., Lexington and Louisville. VPNs provide secure connections to an organization’s network. For best results, a VPN should be configured by an IT professional, whether in-house or a contracted partner, he said.
For other companies, online file-sharing platforms such as Microsoft’s OneDrive or Google Drive might fit the bill. They can be accessed remotely and allow for collaboration among coworkers.
A reliable and secure file-sharing program is vital, says Lexington-based Integrity IT, now called The Ame Group.
No matter how employees access company data, whether via VPN or an internet-based storage platform, multi-factor authentication (MFA) should be required in all remote-access scenarios, Cozzi said. This provides an extra layer of security to keep hackers from accessing accounts.
With MFA, users are only granted access if they can provide two or more different types of credentials to an authentication mechanism. (Examples of the credentials are password or PIN; something you possess, such as the device you’re using; and/or a characteristic that is unique to you – biometrics like a fingerprint, an iris scan, your voice.)
Encryption technologies should be used to protect communications and data stored, SimplifIT said. All devices used by employees to access company data should be encrypted.
Robust password management also is a must, the company said. Use passwords that include a mix of upper and lowercase letters, symbols and numbers, or better yet, use a password manager program, which helps users generate unique password and stores in them in an encrypted place.
Lorie Hailey is Special Publications Editor for The Lane Report. Contact her at [email protected]













Add Comment